
- Home
- Managed Services
- Cyber Security
- Blog
- About Us

We 365 Admin Support, just simplify your IT problems
Call for a free support. +91 96666 59505Platform Partnership
- Who We Help
- Shop
- Contact
- News




Recently, an ASUS Live Update vulnerability identified as CVE-2025-59374 has gained attention in cybersecurity discussions, with some reports suggesting active exploitation.
This CVE references an older supply-chain attack involving an End-of-Life (EoL) software product, rather than presenting a new threat.
Table of Contents
ToggleMedia coverage surrounding CVE-2025-59374 has characterized it as a pressing security concern after its addition to CISA’s Known Exploited Vulnerabilities (KEV) catalog.
However, a closer examination reveals a more intricate reality.
The CVE outlines the 2018-2019 “ShadowHammer” supply-chain attack, which involved maliciously altered ASUS Live Update binaries that were distributed to select targeted systems.
The CVE entry regarding the compromise, currently rated a 9.3 (Critical) on the CVSS scale, states:
“UNSUPPORTED WHEN ASSIGNED” Certain versions of the ASUS Live Update client were distributed with unauthorized modifications introduced through a supply chain compromise. The modified builds could cause devices meeting specific targeting conditions to perform unintended actions. Only devices that met these conditions and installed the compromised versions were affected. The Live Update client has already reached End-of-Support (EOS) in October 2021, and no currently supported devices or products are affected by this issue.
The phrase ‘unsupported when assigned‘ implies that this CVE was filed for an EoL product.
The main vendor advisory linked to the CVE entry dates back to 2019, and includes an FAQ: https://www.asus.com/support/faq/1018727/ that was last updated on 2025/12/06 20:09.
Importantly, this FAQ link was already present in 2019 when the original advisory was published.
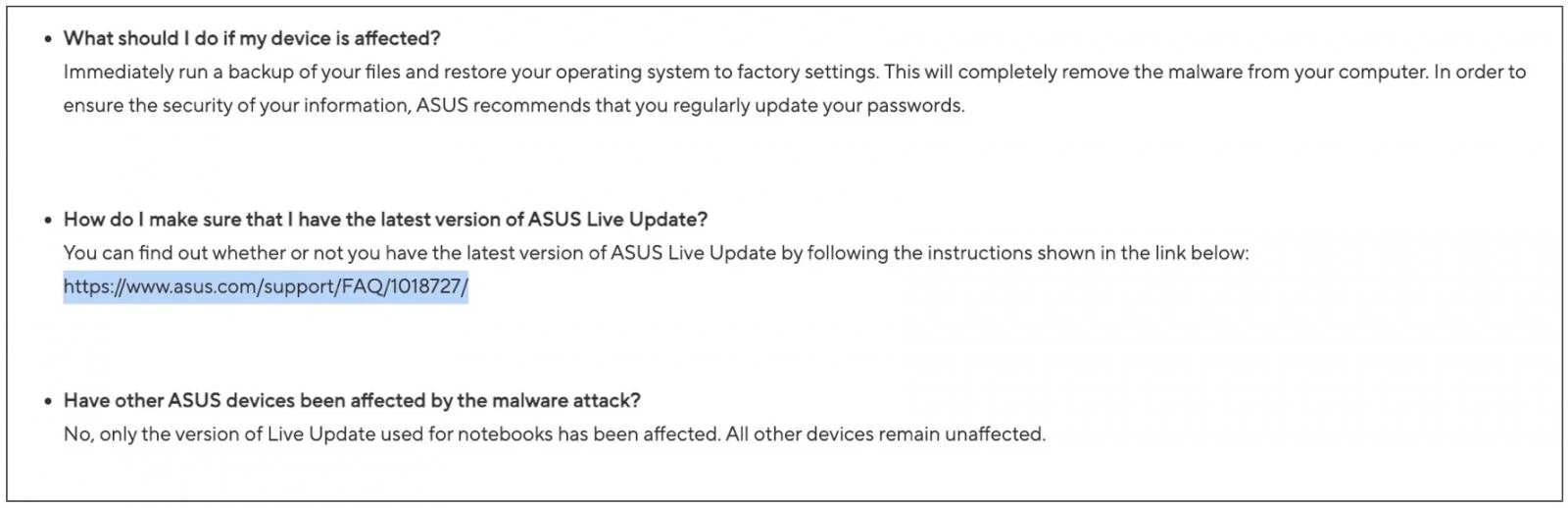
According to BleepingComputer, the FAQ page lacks the initial publication date metadata. It was simply revised this month, showing the mentioned December 6th date.
The archived versions help clarify the page’s purpose and why the recent updates do not necessarily signal a renewed risk from the 2019 incident.
The FAQ appears to serve as ASUS’ placeholder page, periodically updated to inform users about the latest version of the Live Update utility they should use.
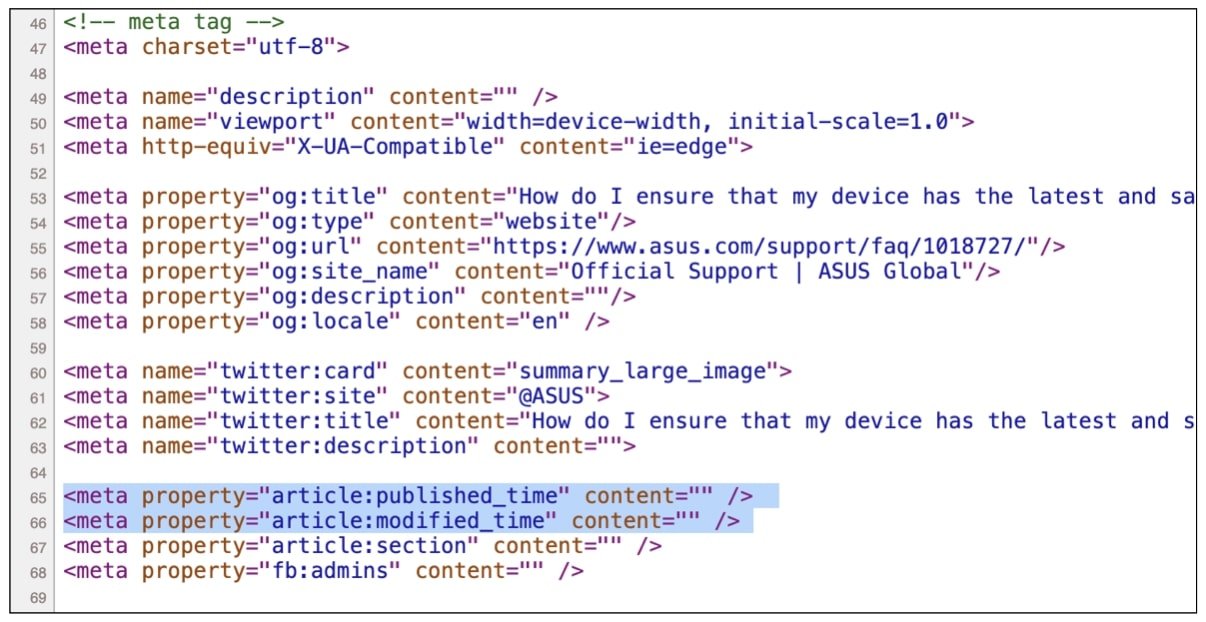
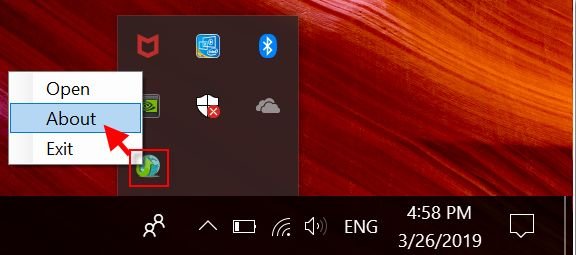
Additionally, the webpage continues to show older remediation guidance with screenshots dated 2019:
For more clarity on the 2025 CVE classification, BleepingComputer reached out to ASUS before publication but did not receive a response.
We also contacted CISA to inquire about the decision to add the CVE to the KEV catalog.
CISA declined to provide more information, directing BleepingComputer to wording in the Binding Operational Directive 22-01, which states:
“The addition of a vulnerability to the KEV catalog does not imply that CISA is observing current active exploitation. If there is accurate reporting of active exploitation, any vulnerability, regardless of its age, can qualify for KEV catalog addition.”
This evidence suggests the CVE designation represents a retrospective classification, formally recognizing an already well-known attack that predated the CVE’s issuance.
Users should ensure they have the latest patched version of the product.
The CVE entry indicates that the ASUS Live Update software reached End-of-Support (EOS) in October 2021, and no currently supported products are affected by this issue.
The updated ASUS FAQ page, however, contradicts this statement, suggesting that support definitively ended on December 4, 2025:
“We announced end of support for ASUS LiveUpdate on 2025/12/4, the last version is 3.6.15.“
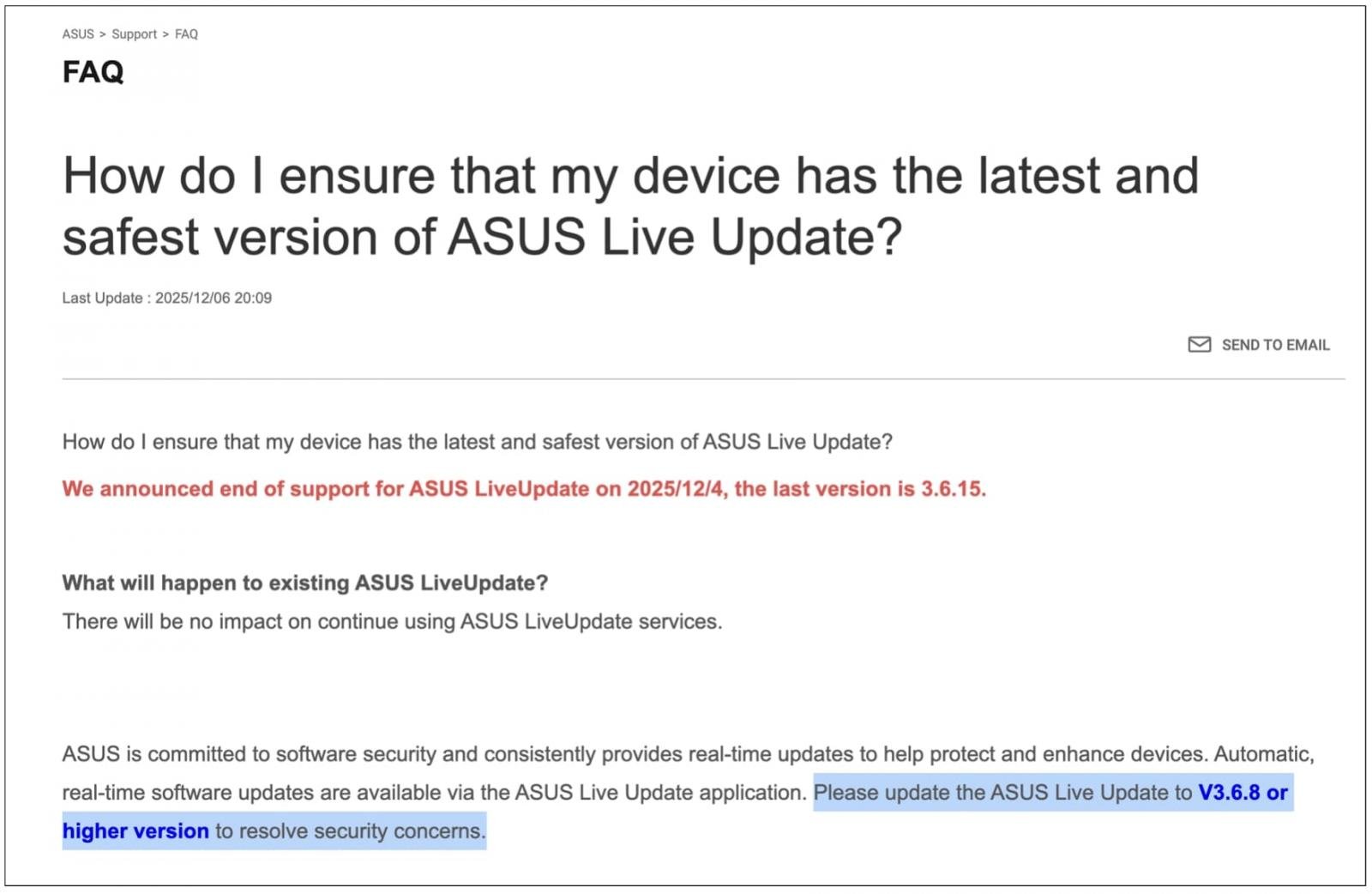
Previous versions of the FAQ recommended upgrading to “V3.6.8 or higher version to resolve security concerns,” as a fix was implemented in that version back then. That outdated guidance remains unchanged on the updated FAQ from this month.
Although release 3.6.15 is now classified as the “last version,” it seemingly existed as early as March 2024, suggesting there is no immediate urgency for an upgrade—contrary to typical reactions following recent supply chain incidents.
The CVE-2025-59374 serves to formalize a historically documented attack. Updates on the FAQ, earlier remediation advice, the latest utility release, and CISA’s contextual information indicate that the page revisions were made for documentation purposes, rather than responding to a new exploit, enforcing patching mandates, or signaling immediate risk.
Therefore, security teams should exercise caution when interpreting CISA-associated CVEs as urgent, especially in relation to discontinued software or previously settled issues.