
- Home
- Managed Services
- Cyber Security
- Blog
- About Us

We 365 Admin Support, just simplify your IT problems
Call for a free support. +91 96666 59505Platform Partnership
- Who We Help
- Shop
- Contact
- News




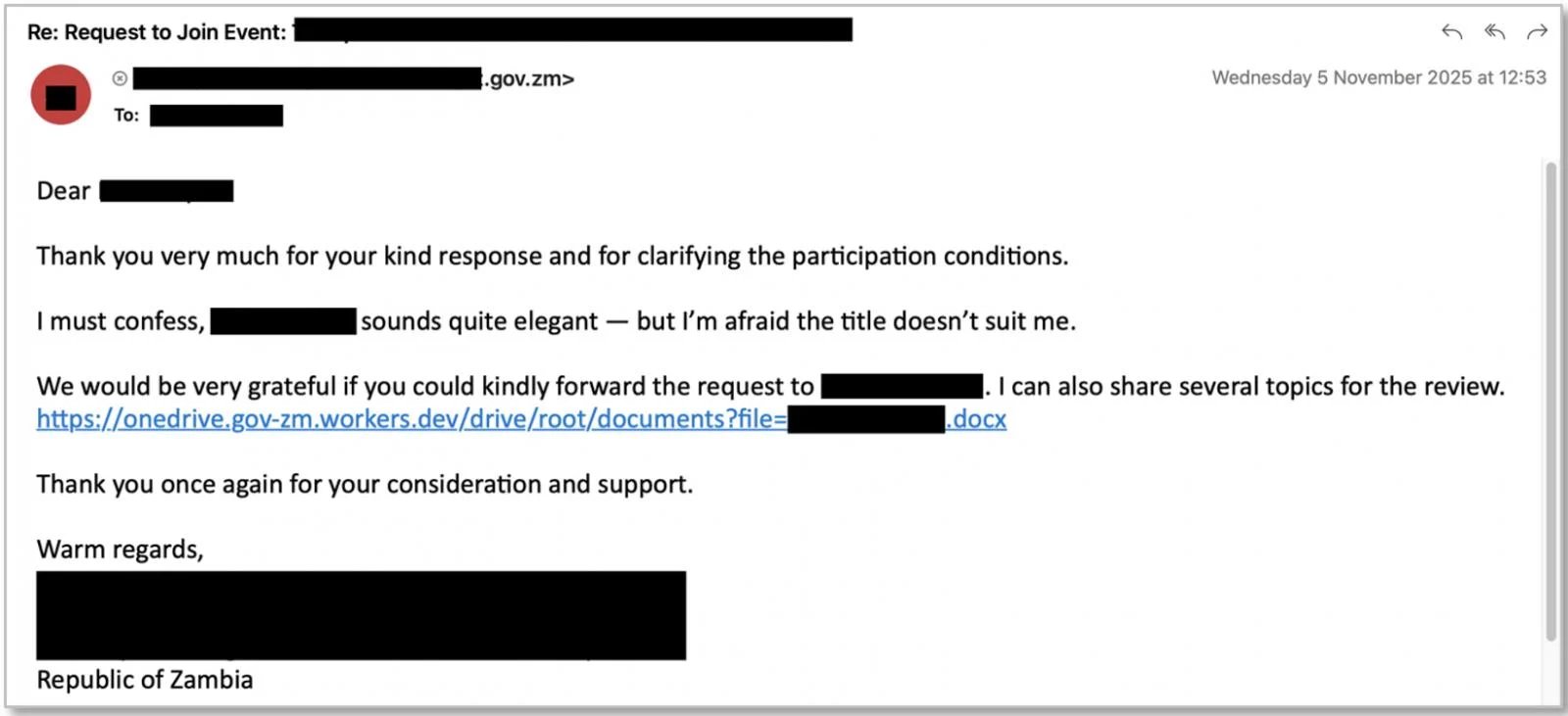
A variety of threat actors are exploiting Microsoft 365 accounts through phishing attacks utilizing the OAuth device code authorization system.
In these attacks, victims are misguided into entering a device code on Microsoft’s authentic login page, unintentionally granting access to an attacker-controlled application. This enables attackers to access the target account without needing to steal credentials or circumvent multi-factor authentication (MFA).
While this technique is not novel, Proofpoint, an email security firm, indicates that there has been a notable rise in such attacks since September. Both financially-motivated cybercriminals like TA2723 and state-sponsored actors are involved.
“Proofpoint Threat Research has noted multiple threat clusters utilizing device code phishing to deceive users into providing attackers access to their Microsoft 365 account,” the firm cautioned. They remarked that widespread campaigns employing these methods are “highly unusual.”
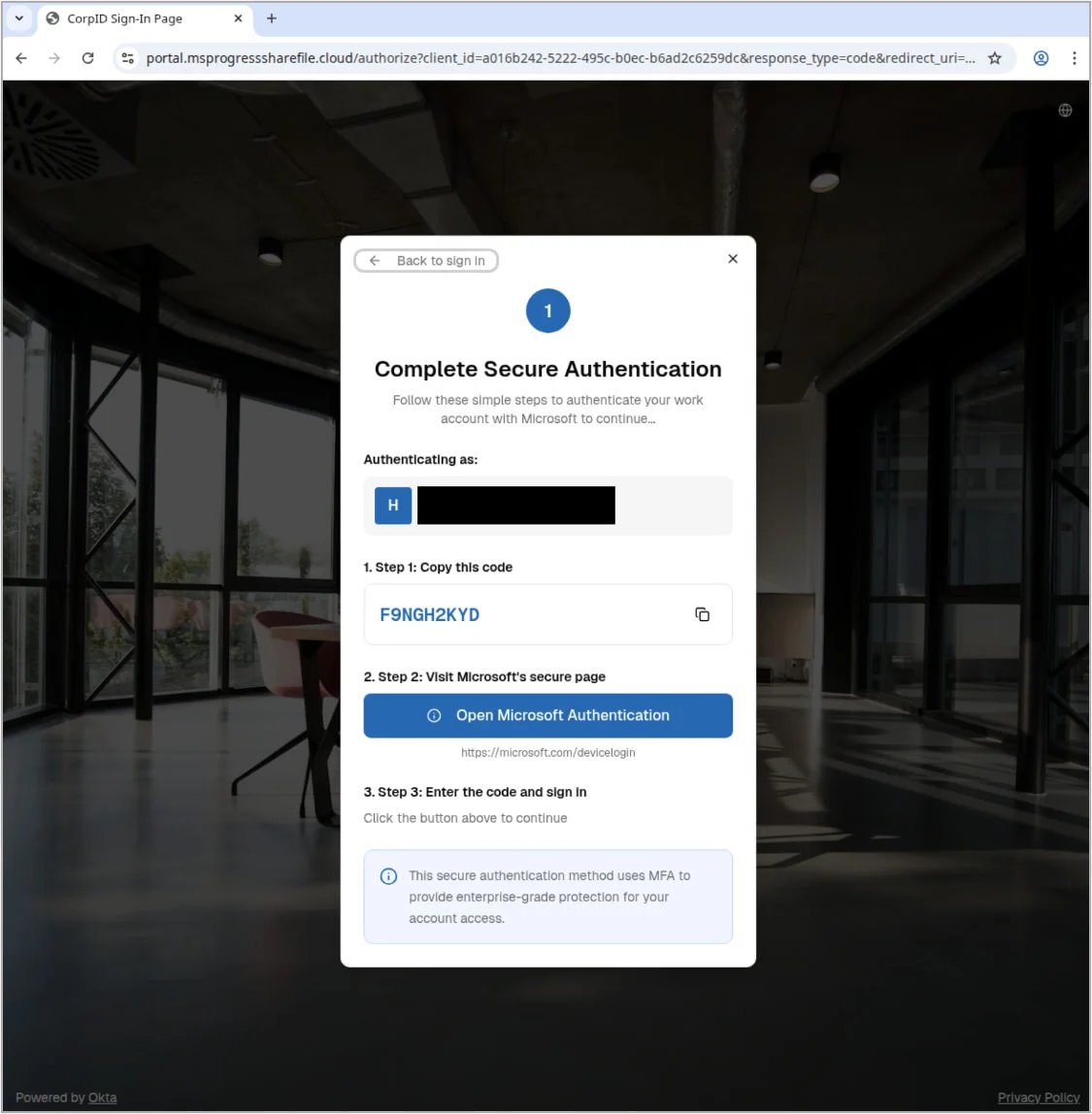
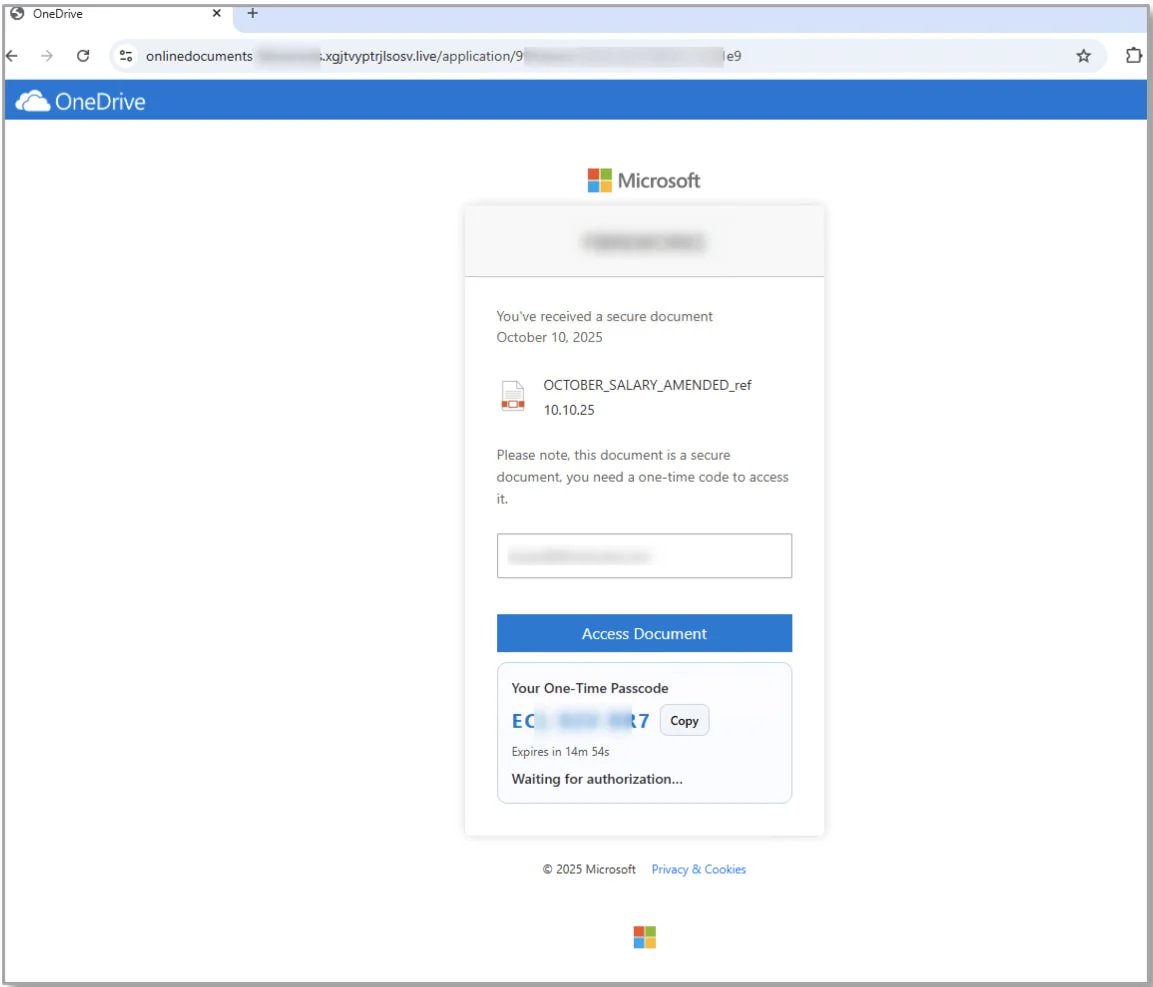
The attack chains observed by Proofpoint exhibit slight variations, yet all have a common thread: they deceive victims into entering device codes on Microsoft’s legitimate login portals.
In certain instances, the device code appears as a one-time password. Other variations may involve notifications for token reauthorization.
Researchers identified two phishing kits used in these attacks: SquarePhish v1 and v2, as well as Graphish, which streamline the phishing operation.
SquarePhish is a publicly accessible red teaming tool targeting OAuth device grant authorization flows through QR codes, closely mimicking legitimate Microsoft MFA/TOTP setups.
Graphish is a malicious phishing kit that has been circulated in underground forums, facilitating OAuth abuse, Azure App Registrations, and adversary-in-the-middle (AiTM) attacks.
In terms of the campaigns observed by Proofpoint, three were highlighted in the report:
To combat these attacks, Proofpoint advises organizations to utilize Microsoft Entra Conditional Access where feasible and to consider implementing policies regarding sign-in origin.
Broken IAM isn’t just an IT challenge – the repercussions extend throughout your entire organization.
This practical guide explores why traditional IAM practices struggle to meet modern needs, showcases what effective IAM looks like, and provides a straightforward checklist for developing a scalable strategy.