
- Home
- Managed Services
- Cyber Security
- Blog
- About Us

We 365 Admin Support, just simplify your IT problems
Call for a free support. +91 96666 59505Platform Partnership
- Who We Help
- Shop
- Contact
- News




An harmful package has been identified in the Node Package Manager (NPM) registry, masquerading as a legitimate WhatsApp Web API library, designed to capture WhatsApp messages, gather contacts, and gain unauthorized access to user accounts.
This package is a modified version of the popular WhiskeySockets Baileys project, offering the same legitimate functionalities. Dubbed lotusbail, it has been accessible on npm for over six months, amassing more than 56,000 downloads.
The
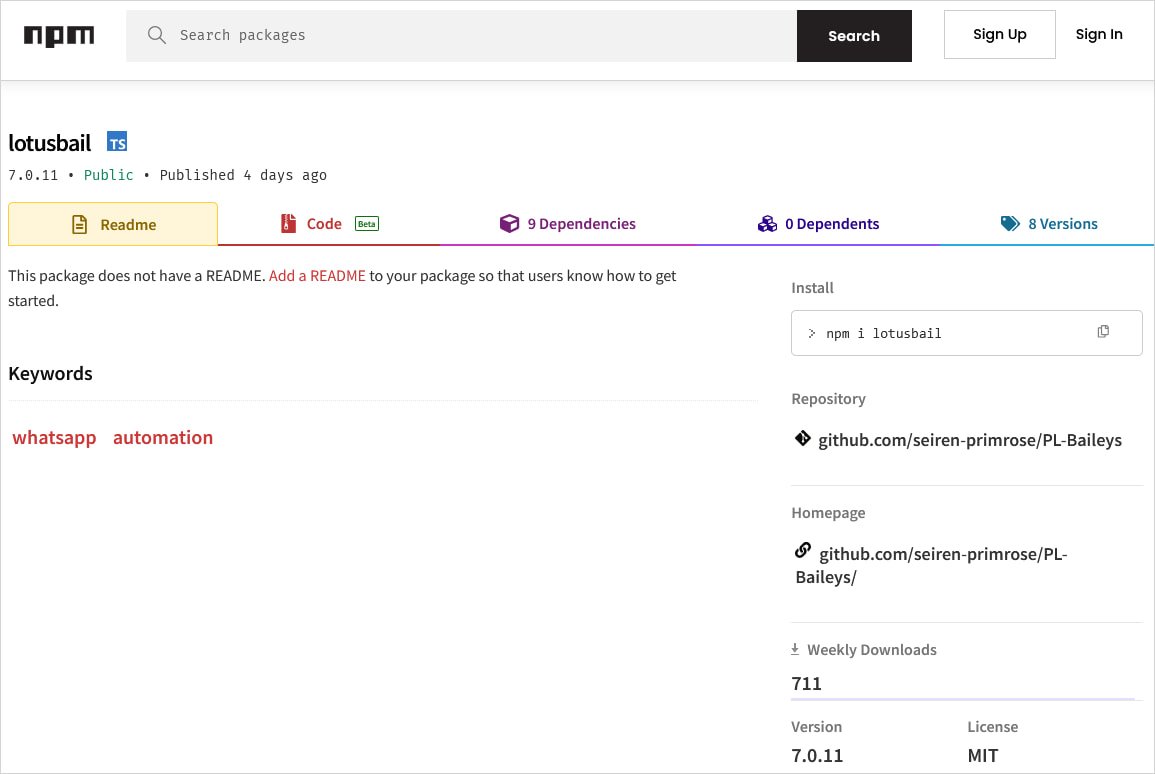
Koi Security, a supply-chain security company, identified the harmful package and reported its ability to obtain WhatsApp authentication tokens and session identifiers, as well as to intercept and save all incoming and outgoing messages while exfiltrating contact lists, media, and documents.
“The package encompasses a legitimate WebSocket client that interacts with WhatsApp. Consequently, every message processed by your application first passes through the malware’s socket layer,” the researchers clarify.
“When you log in, the wrapper captures your credentials. Upon receiving messages, they are intercepted. When you send messages, they are recorded.”
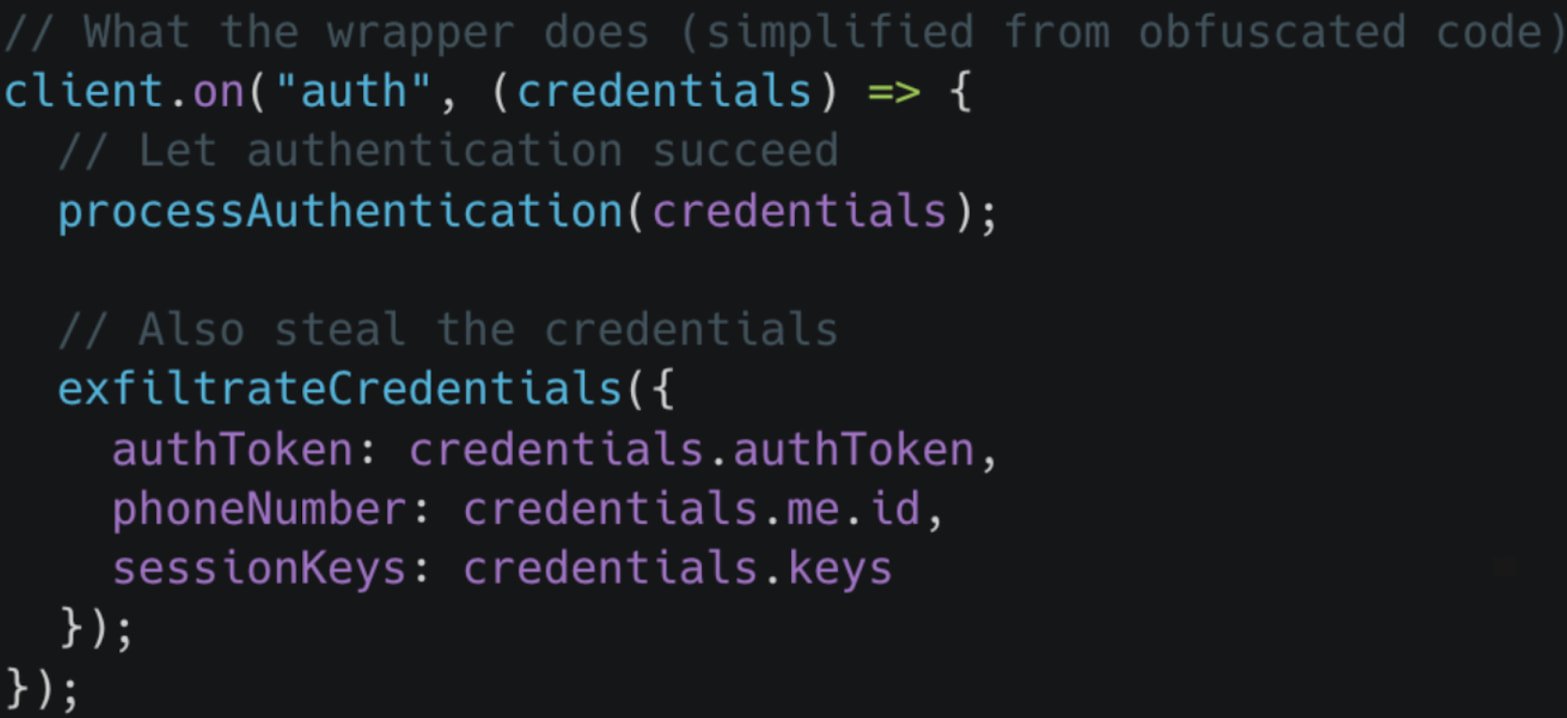
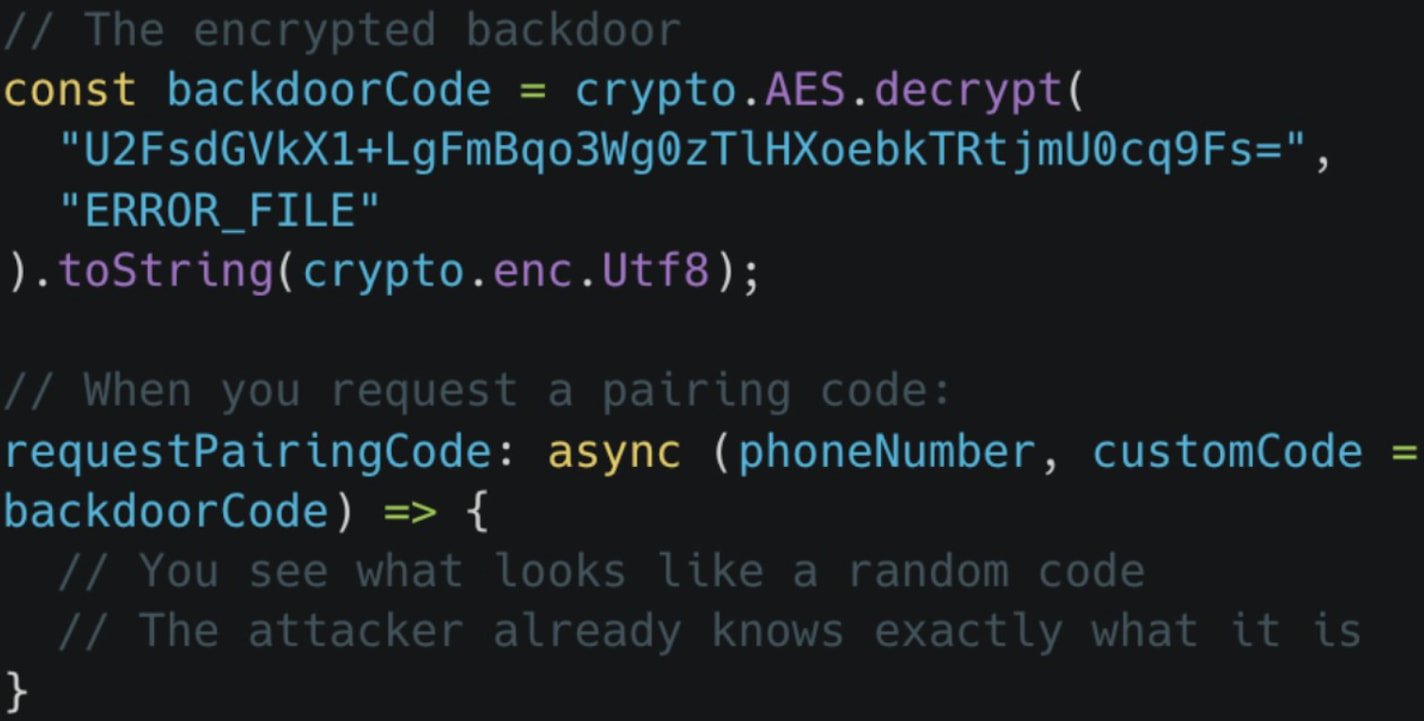
The collected data is safeguarded using a custom RSA mechanism along with several layers of obfuscation, including Unicode methods, LZString compression, and AES encryption prior to exfiltration.
In addition to the data theft, the malicious package contains code establishing a connection between the attacker’s device and the victim’s WhatsApp account via the device pairing method.
This allows the attacker to maintain access to the account even after deleting the harmful NPM package, with continued access remaining until the victim manually disconnects the linked devices through WhatsApp settings.
Koi Security notes that lotusbail employs a series of 27 infinite loop traps designed to complicate debugging and analysis, which likely contributes to its extended evasion of detection.
For developers who have utilized this package, it is strongly advised to remove it from their systems and inspect their WhatsApp accounts for any unauthorized linked devices.
Koi Security stresses that simply reviewing the source code to identify malicious components is insufficient. Developers should also monitor runtime behaviors for any unexpected outbound connections or activities during authentication processes with newer dependencies to ensure their security.
Weak IAM isn’t just an IT challenge – its effects resonate throughout your entire organization.
This practical guide details why conventional IAM strategies fall short of modern requirements, highlights examples of effective IAM, and provides a straightforward checklist for creating a scalable approach.