
- Home
- Managed Services
- Cyber Security
- Blog
- About Us

We 365 Admin Support, just simplify your IT problems
Call for a free support. +91 96666 59505Platform Partnership
- Who We Help
- Shop
- Contact
- News




Korean Air has recently faced a data breach that has impacted a significant number of its employees, stemming from a cyberattack targeting its in-flight catering supplier and former subsidiary, Korean Air Catering & Duty-Free (KC&D).
The national airline of Korea employs over 20,000 staff members and operates a fleet of approximately 160 aircraft. In 2024, the airline reported revenues exceeding $11 billion while servicing more than 23 million passengers.
An internal notification was released by the airline on Monday, revealing a breach after KC&D notified them of the hack. KC&D became an independent entity focused on in-flight meals and retail in 2020.
“The personal data, including names and bank account information, of our employees stored on the compromised servers was accessed during this incident,” said Woo Kee-hong, CEO of Korean Air, in a memo addressed to staff.
“Despite this breach occurring within the management framework of an external partner that was previously a part of us, we treat this matter with extreme seriousness due to its impact on our employees’ sensitive information.”
While the airline refrained from disclosing the exact number of employees affected, news reports indicate that around 30,000 records were extracted by the cyber attackers.
Korean Air has promptly informed the relevant authorities about the situation. Although there is no evidence at this time that the stolen data has been utilized for fraudulent activities, employees have been advised to remain vigilant against fraudulent messages impersonating the airline.
“Our current priority is to ascertain the full extent and specific targets of this breach. So far, no signs of additional employee information breaches beyond those mentioned have been detected,” Kee-hong stated.
“To avoid possible further damage, we urge all employees to stay alert to suspicious communications, including texts or emails impersonating the company or financial institutions, and requests for security card numbers.”
Korean Air has requested KC&D to perform a comprehensive investigation into the incident’s origins and to implement strict measures to avert future occurrences. A spokesperson for Korean Air assured that the airline remains dedicated to enforcing rigorous internal data security protocols.
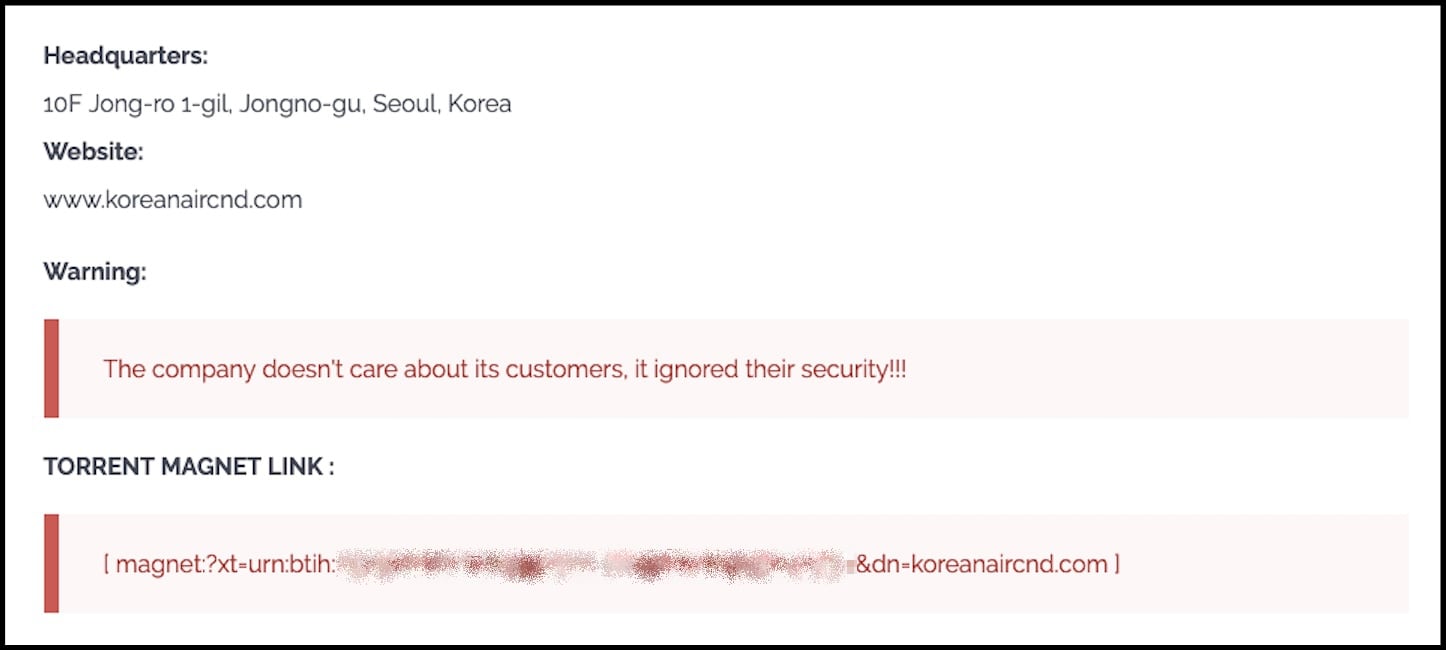
Though Korean Air has not officially linked the attack to any specific group, reports indicate that the Clop ransomware gang claimed responsibility for the KC&D hack in November, subsequently publishing the stolen data on its dark web site for distribution via Torrent.
As part of a broader wave of data theft incidents, Clop has targeted the Oracle EBS systems of numerous organizations worldwide, including GlobalLogic, Logitech, Harvard University, the University of Pennsylvania, The Washington Post, and Envoy Air, leaking confidential data through its leak site.
This ransomware collective has previously targeted a range of systems, including GoAnywhere MFT, Accellion FTA, Cleo, and MOVEit Transfer, and more recently, Gladinet CentreStack.
The U.S. Department of State is currently offering a $10 million bounty for information linking the actions of Clop to any foreign government.
Update December 30, 09:27 EST: Added Korean Air statement.
Broken IAM isn’t just an IT problem – the effects reverberate throughout your entire organization.
This comprehensive guide discusses why traditional IAM approaches often fall short of modern requirements, what exemplary IAM looks like, and provides a straightforward checklist for building an effective strategy.