
- Home
- Managed Services
- Cyber Security
- Blog
- About Us

We 365 Admin Support, just simplify your IT problems
Call for a free support. +91 96666 59505Platform Partnership
- Who We Help
- Shop
- Contact
- News




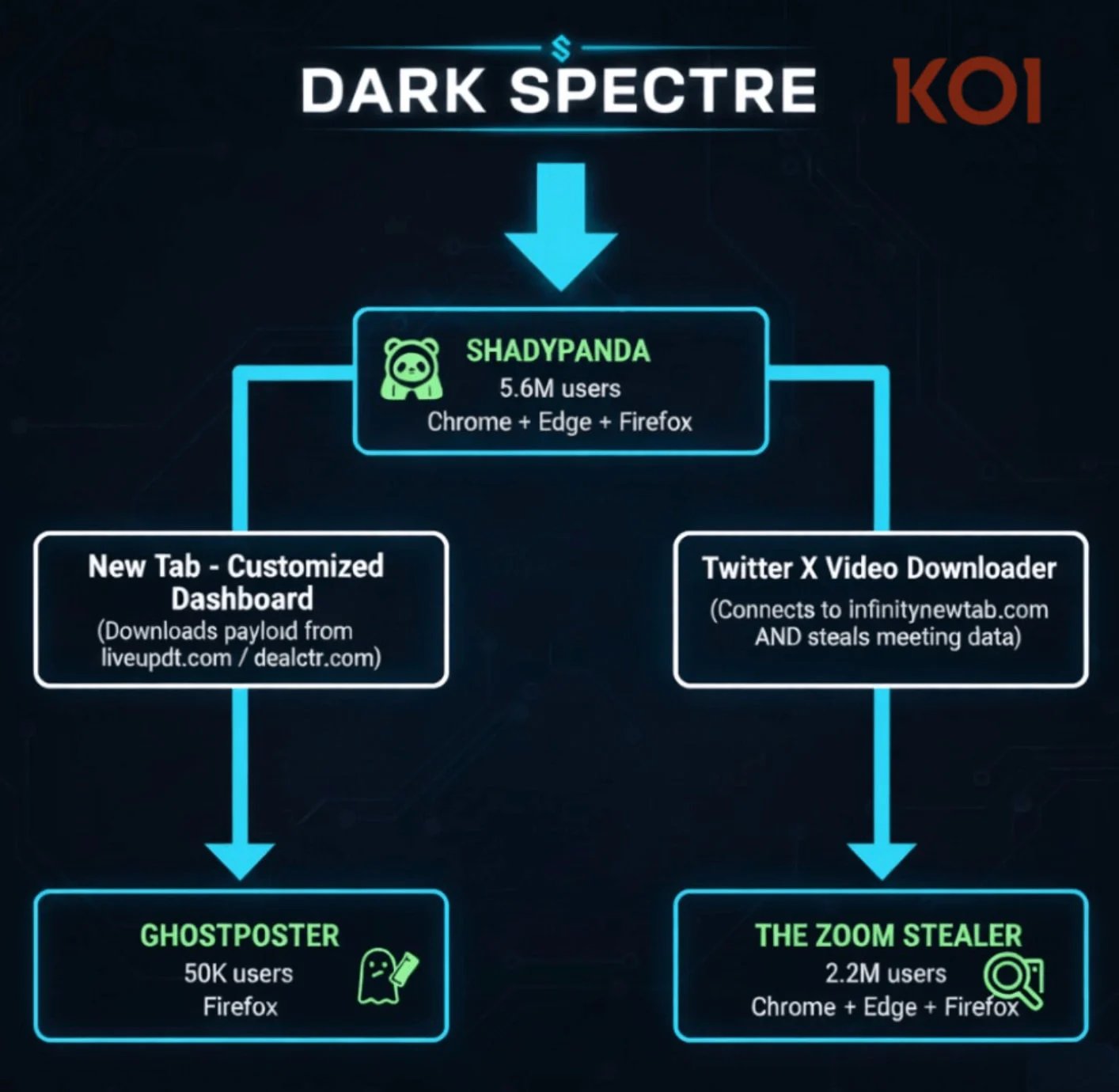
A recently uncovered campaign, dubbed Zoom Stealer, is impacting around 2.2 million users of Chrome, Firefox, and Microsoft Edge through 18 malicious extensions. These extensions are designed to collect critical online meeting-related data, such as URLs, IDs, topics, descriptions, and even embedded passwords.
Zoom Stealer forms part of a broader series of browser extension campaigns that have affected over 7.8 million users in a span of seven years, with all of them linked to a singular threat actor identified as DarkSpectre.
Research indicates that DarkSpectre is likely the same China-associated threat actor responsible for the previously identified GhostPoster, which attacked Firefox users, as well as ShadyPanda, known for delivering spyware to Chrome and Edge browsers.
ShadyPanda continues to operate through nine distinct extensions, along with 85 additional ‘sleepers’ that establish a user base before activating malicious functions through updates, according to researchers at Koi Security.
While the connection to China was previously noted, the attribution has become more evident due to factors such as hosting servers on Alibaba Cloud, ICP registrations, code artifacts with Chinese-language comments, activity patterns aligned with the Chinese timezone, and monetization strategies focused on Chinese e-commerce.
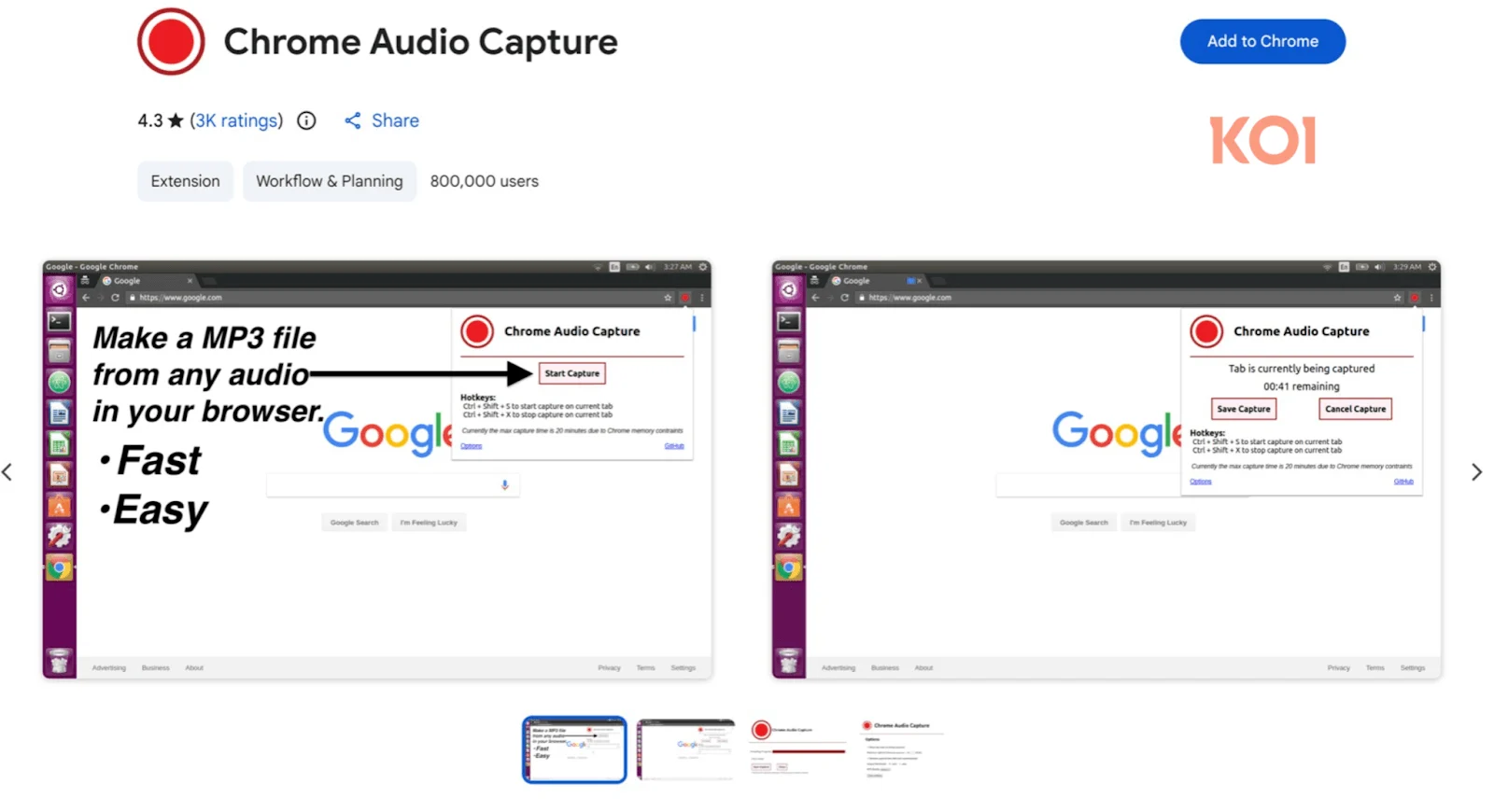
In the Zoom Stealer campaign, not all 18 extensions are solely meeting-related. Some deliver functionalities like video downloading or act as recording assistants, including Chrome Audio Capture, which has around 800,000 installations, as well as Twitter X Video Downloader. At the time of writing, both extensions remain available in the Chrome Web Store.
Researchers from Koi Security emphasize that these extensions are fully functional and perform as advertised.
As per the findings, all extensions involved in the Zoom Stealer operation seek access to 28 video-conferencing platforms (such as Zoom, Microsoft Teams, Google Meet, and Cisco WebEx) and gather various types of data, including:
This information is sent out via WebSocket connections and is streamed to the threat actors in real-time, triggered when victims visit registration pages, join meetings, or navigate through conferencing platforms.
Koi Security warns that this data has potential uses in corporate espionage or sales intelligence, which could facilitate social engineering attacks or even allow for the sale of meeting links to competitors.
“By systematically compiling meeting links, participant lists, and corporate intelligence from 2.2 million users, DarkSpectre has built a database capable of powering extensive impersonation operations – giving attackers credentials to access confidential calls, participant lists to know whom to impersonate, and context to make those impersonations believable,” states the Koi Security report.
As many of these extensions run smoothly for extended periods, users are advised to review the permissions demanded by their extensions and minimize the number they use to the essential minimum.
Koi Security has reported the offending extensions, yet many are still present on the Chrome Web Store. The researchers have also published a comprehensive list of the active DarkSpectre extensions.
BleepingComputer has reached out to InfinityNewTab and Google for comments and will update this article upon receiving a response.
Inadequate Identity Access Management (IAM) isn’t solely an IT issue—its consequences extend throughout your entire organization.
This practical guide explains why conventional IAM practices fall short in today’s landscape, provides examples of what effective IAM entails, and offers a straightforward checklist for developing a scalable strategy.