
- Home
- Managed Services
- Cyber Security
- Blog
- About Us

We 365 Admin Support, just simplify your IT problems
Call for a free support. +91 96666 59505Platform Partnership
- Who We Help
- Shop
- Contact
- News




A recent sample of the ToneShell backdoor, commonly associated with Chinese cyberespionage operations, has been deployed using a kernel-mode loader in cyberattacks against governmental entities.
The backdoor has been linked to the Mustang Panda group, which is also referred to as HoneyMyte or Bronze President, and typically targets government agencies, NGOs, think tanks, and various prestigious organizations globally.
Security analysts at Kaspersky discovered a malicious driver on systems in Asia, which has been linked to campaigns targeting government organizations in Myanmar, Thailand, and other regions of Asia since at least February 2025.
Evidence suggests that targeted organizations had previously suffered infections from older variants of ToneShell, PlugX malware, or the ToneDisk USB worm, which are also linked to state-sponsored Chinese hackers.
Table of Contents
ToggleKaspersky reports that the new ToneShell backdoor was introduced via a mini-filter driver known as ProjectConfiguration.sys, which was signed with a stolen or leaked certificate that was valid from 2012 to 2015 and issued to Guangzhou Kingteller Technology Co., Ltd.
Mini-filter drivers operate in kernel mode in the Windows I/O file system stack, allowing them to inspect, modify, or block file operations. They are commonly utilized by security software, encryption applications, and backup utilities for various purposes.
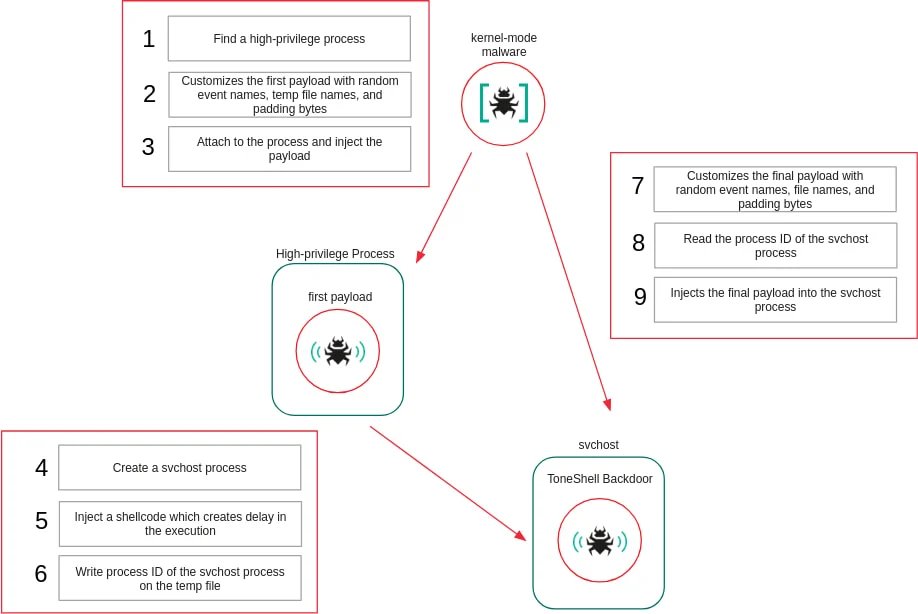
ProjectConfiguration.sys contains two user-mode shellcodes in its .data section, each executed as separate threads that get injected into user-mode processes.
In order to avoid static analysis detection, the driver dynamically resolves essential kernel APIs by enumerating loaded kernel modules and matching function hashes rather than importing functions directly.
It registers as a mini-filter driver and intercepts file system operations involving deletion and renaming. When these operations attempt to target the driver itself, they are thwarted by enforcing failure on the requests.
Additionally, it protects its service-related registry keys through a registry callback that blocks attempts to create or access them. To ensure superiority over security products, the driver selects a mini-filter altitude that surpasses that reserved for antivirus products.
The rootkit also interferes with Microsoft Defender by altering the WdFilter driver configuration to prevent it from loading into the I/O stack.
To protect injected user-mode payloads, the driver keeps a list of protected process IDs, denying access to those processes while the payloads are active, and lifting that protection once execution concludes.
“This marks the first instance of ToneShell being deployed via a kernel-mode loader, thus gaining protection from user-mode monitoring and leveraging the rootkit capabilities of the driver to conceal its activities from security tools,” states Kaspersky.
The latest variant of the ToneShell backdoor analyzed by Kaspersky introduces changes and enhancements for stealth. This version employs a new host identification format based on a 4-byte host ID instead of the previous 16-byte GUID, and it utilizes network traffic obfuscation, incorporating fake TLS headers.
Regarding the supported remote operations, the backdoor is capable of executing the following commands:
Kaspersky emphasizes that memory forensics are crucial for uncovering ToneShell infections enhanced by the new kernel-mode injector.
Researchers are confident in their attribution of the new ToneShell backdoor sample to the Mustang Panda cyberespionage group, suggesting that the threat actor has advanced its tactics, techniques, and procedures for greater operational stealth and durability.
The cybersecurity firm includes a brief list of indicators of compromise (IoCs) in its report to assist organizations in identifying Mustang Panda intrusions and enhancing their defenses.