
- Home
- Managed Services
- Cyber Security
- Blog
- About Us

We 365 Admin Support, just simplify your IT problems
Call for a free support. +91 96666 59505Platform Partnership
- Who We Help
- Shop
- Contact
- News




WebRAT malware is currently being distributed through GitHub repositories that falsely claim to offer proof-of-concept exploits for recently identified vulnerabilities.
This malware, which was previously distributed via pirated software and cheats for games such as Roblox, Counter Strike, and Rust, is a backdoor capable of stealing information and has been active since the start of the year.
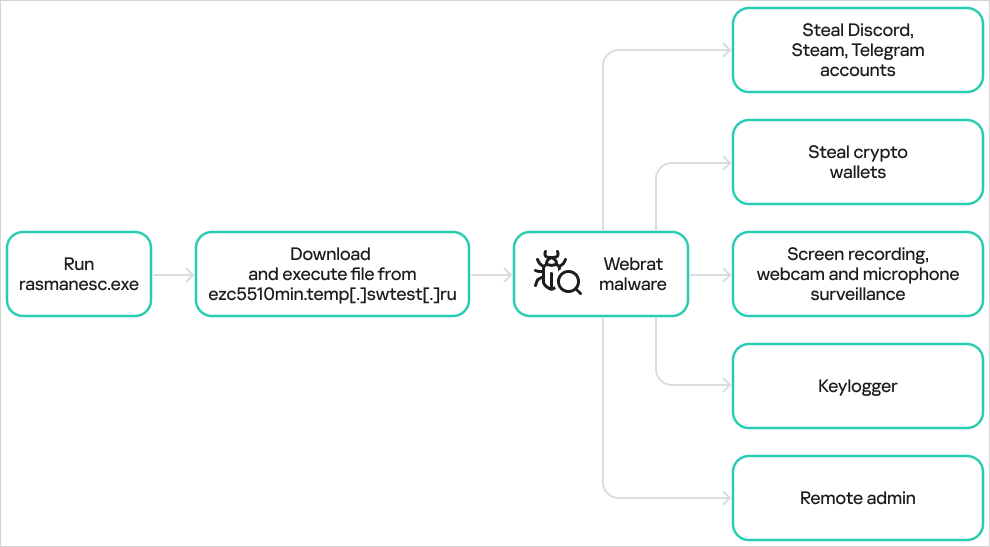
A report from Solar 4RAYS indicated in May that WebRAT can extract credentials from Steam, Discord, and Telegram accounts in addition to cryptocurrency wallet details. Moreover, it has the ability to surveil victims using webcams and can also take screenshots.
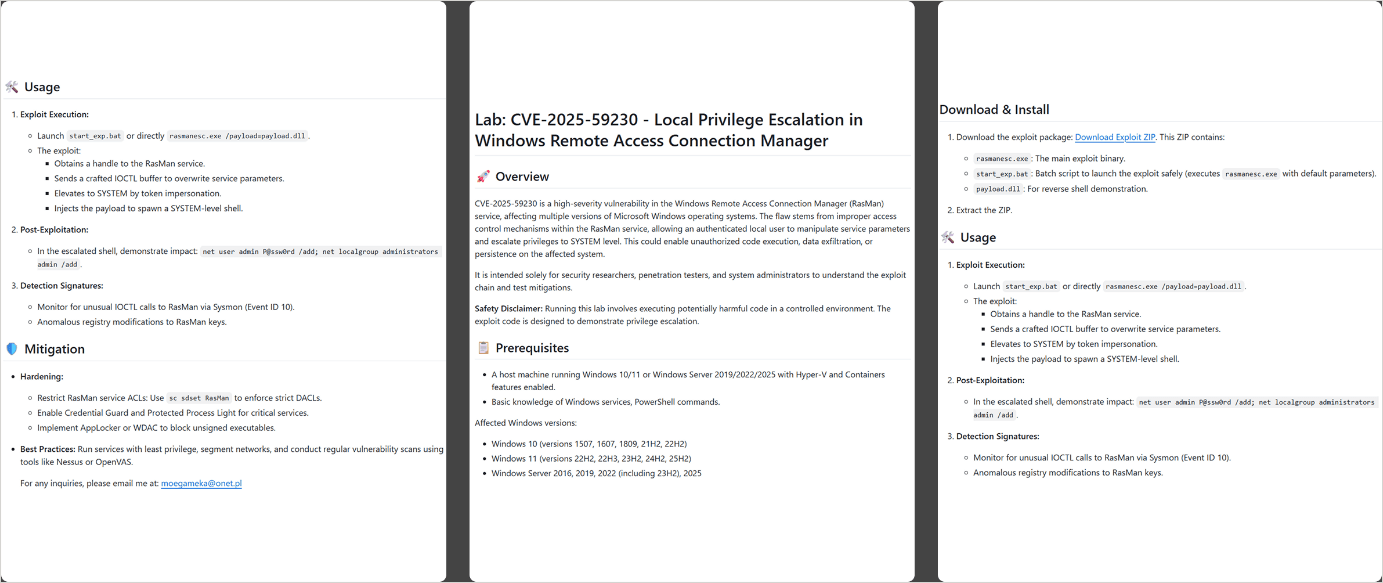
As early as September, the operators began to deploy the malware through meticulously crafted repositories claiming to offer exploits for various vulnerabilities that had garnered media attention. Some of these include:
Researchers at Kaspersky identified 15 repositories propagating WebRAT, all of which provided information about the vulnerabilities, the supposed exploits, and available mitigations.
Based on the structured presentation of this information, Kaspersky suspects it was generated using an AI model.
The malware operates using several methods to maintain persistence, including modifications to the Windows Registry, leveraging the Task Scheduler, and injecting itself into various system directories.
Kaspersky’s analysis indicates that the counterfeit exploits are packaged within a password-protected ZIP file containing an empty file named after the password, a corrupted DLL file acting as a diversion, a batch file for execution, and the main dropper named rasmanesc.exe.
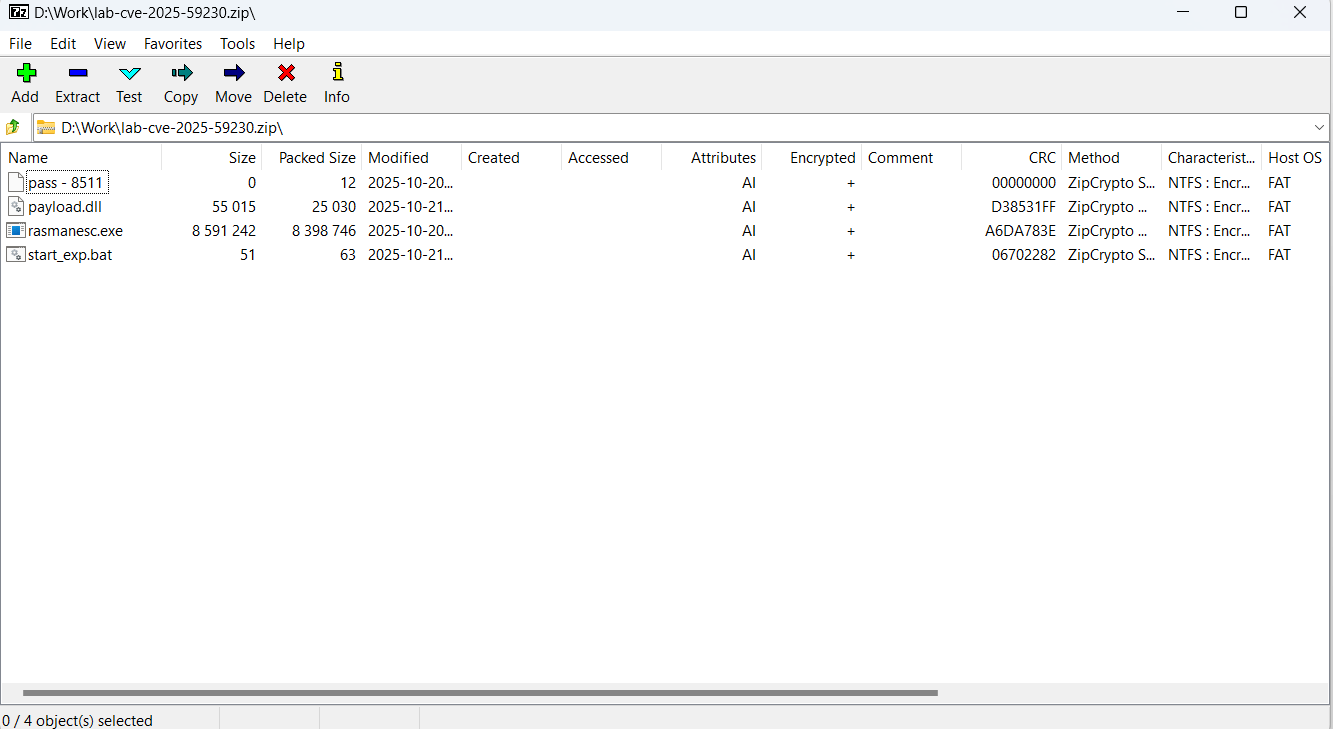
According to the analysts, this dropper elevates system privileges, disables Windows Defender, and subsequently downloads and executes WebRAT from a hardcoded URL.
Kaspersky reports that this variant of WebRAT is consistent with older samples and retains the same capabilities documented in previous reports.
The tactic of using fraudulent exploits on GitHub to trick users into installing malware isn’t novel, having been thoroughly documented in the past [1, 2, 3, 4]. Recently, a phony “LDAPNightmare” exploit was promoted on GitHub to propagate infostealing malware.
Kaspersky has removed all malicious GitHub repositories associated with the WebRAT campaign; however, developers and infosec professionals should exercise caution regarding the sources they utilize, as attackers may present new lures under different publisher identities.
The best practice when testing exploits or code from potentially untrusted sources is to conduct tests in a controlled, isolated environment.
Issues with IAM aren’t solely an IT concern; the repercussions extend throughout the entire organization.
This practical guide explores why traditional IAM methods fall short in meeting contemporary requirements, showcases examples of effective IAM strategies, and includes a straightforward checklist for establishing a scalable approach.