
- Home
- Managed Services
- Cyber Security
- Blog
- About Us

We 365 Admin Support, just simplify your IT problems
Call for a free support. +91 96666 59505Platform Partnership
- Who We Help
- Shop
- Contact
- News



Coupang, the foremost e-commerce platform in South Korea, has recently revealed a data breach that impacts 33.7 million customer accounts, representing almost two-thirds of the country’s population.
This breach marks the largest e-commerce security incident in South Korean history and could incur fines up to $900 million (around 1.2 trillion KRW).
The incident has exposed significant weaknesses in data protection frameworks, especially for e-commerce platforms that manage sensitive information such as transaction records, delivery addresses, and payment options.
The extent of this breach has caused alarm among customers and industry experts.
Table of Contents
ToggleOn November 29, Coupang confirmed the unauthorized exposure of usernames, phone numbers, email addresses, delivery addresses, and purchase histories.
The company identified abnormal access on November 6 at 6:38 PM KST, but it wasn’t until November 18 at 10:52 PM that the breach was completely understood—over 12 days later.
Investigations showed that hackers had been accessing customer data through overseas servers for nearly five months, from June 24 to November 8.
A former Coupang employee is under investigation as a primary suspect. This individual had access to authentication services and kept access keys long after leaving the company, which facilitated the breach.
The leaked data was not required to be encrypted under South Korean law. As it stands, the Personal Information Protection Act only mandates encryption for payment details such as credit card numbers and unique identifiers like resident registration numbers.
While data points like names, addresses, phone numbers, and purchase histories may appear less critical, they can pose security risks when combined.
Analyzing purchase histories can reveal lifestyle choices and family details, which, when associated with personal identifiers, could lead to spear-phishing attacks or even physical confrontations.
Additionally, correlating this data with previously compromised payment information can lead to pinpointing individual identities in re-identification attacks.
Just one data breach can erode customer trust, lead to severe regulatory fines, and stall operations for recovery.
Mitigate risks by implementing encryption with D.AMO before it’s too late.
This breach underscores the critical need for data encryption, even in the absence of legal requirements. Unlike unprotected data, which can be easily exploited once compromised, encrypted information remains harmless without the respective decryption keys.
Nonetheless, many organizations deprioritize voluntary encryption in the absence of legal directives.
To mitigate risks from data breaches, firms must integrate proven encryption measures from reputable cybersecurity vendors. Established in 1997, Penta Security has become a global authority in data protection.
In 2004, Penta Security launched D.AMO, a robust data encryption platform featuring encryption capabilities, centralized management, and an independent key management system (KMS).
Over two decades, D.AMO has been implemented by over 10,000 enterprises, including major financial institutions and large corporations, solidifying its stature in global cybersecurity.
D.AMO supports various encryption methods—API-based, plug-in, and kernel-level encryption—without the need for application alterations. This flexibility allows for swift deployment, cutting setup times from months to just days. It also integrates security features like access control, auditing, and monitoring.

Concerns regarding performance degradation due to encryption are valid, but modern technology effectively addresses these issues.
D.AMO, for example, minimizes performance impacts by utilizing column-level selective encryption based on data sensitivity, ensuring compatibility with all layers of an organization’s system landscape.
The Coupang incident surpasses the previous SK Telecom breach involving 27 million users, which resulted in a fine of 134.8 billion KRW.
Under South Korea’s revised data protection laws, penalties can reach 3% of annual revenue, meaning Coupang could face fines ranging from 150 billion KRW up to a staggering 1.2 trillion KRW.
Just days after the breach announcement, class action movements mobilized, with over 200,000 individuals joining discussions in online forums. It’s important to note that the breach stemmed from insider misuse of valid credentials rather than an external cyberattack.
The extended detection duration might also suggest non-compliance with required safety measures, potentially leading to further sanctions.
The Coupang data breach makes it clear that even unregulated information can pose risks when combined. Companies should secure customer data beyond the legal requirements by adopting encryption tools from established cybersecurity companies like Penta Security.
Additionally, organizations require centralized management and robust key management systems.
With nearly three decades of experience and ongoing innovation, Penta Security delivers cybersecurity solutions across various IT infrastructures, including on-premises systems, cloud, multi-cloud, and hybrid setups.
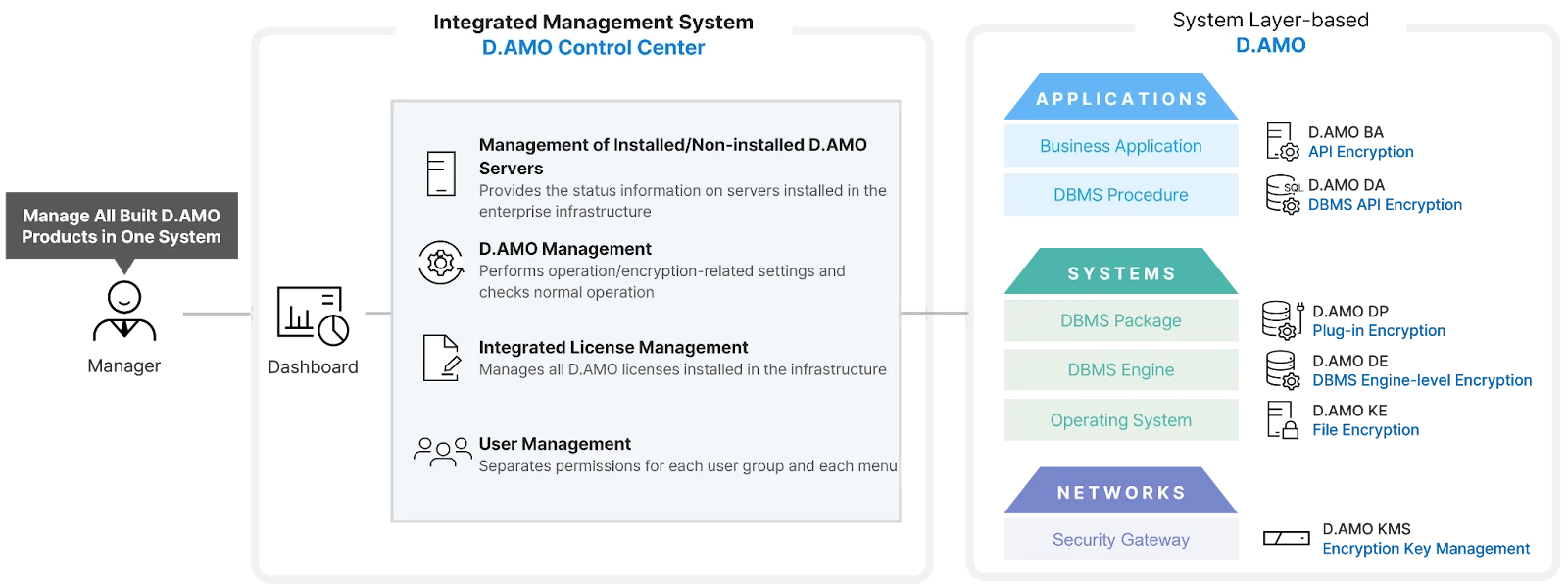
Moreover, Penta Security’s D.AMO can encrypt all data types (both structured and unstructured) and is deployable across all layers of IT systems, such as operating systems, databases, and applications.
The Coupang incident illustrates that organizations may greatly benefit from implementing encryption beyond legally required data to avert similar occurrences.
Sponsored and crafted by Penta Security.