
- Home
- Managed Services
- Cyber Security
- Blog
- About Us

We 365 Admin Support, just simplify your IT problems
Call for a free support. +91 96666 59505Platform Partnership
- Who We Help
- Shop
- Contact
- News




More than 115,000 WatchGuard Firebox devices currently exposed online remain without patches for a serious remote code execution (RCE) vulnerability that is being actively exploited.
This security vulnerability, designated as CVE-2025-14733, impacts Firebox firewalls that are operating on Fireware OS versions 11.x and later (including version 11.12.4_Update1), 12.x or later (including 12.11.5), as well as version 2025.1 up to and including 2025.1.3.
If successfully exploited, attackers can execute arbitrary code remotely on affected devices with minimal complexity and without requiring any user interaction.
As noted in an advisory from WatchGuard, they announced CVE-2025-14733 updates and confirmed its exploitation in the wild. Notably, unpatched Firebox firewalls are only subject to these attacks if they are configured to use IKEv2 VPN. Furthermore, the advisory warns that even if such vulnerable configurations are eliminated, the firewall could still face threats if there exists a Branch Office VPN (BOVPN) to a static gateway peer.
“The iked process within WatchGuard Fireware OS contains an out-of-bounds write vulnerability,” an NVD advisory describes. “This vulnerability allows a remote attacker to execute arbitrary code without authentication and affects both the mobile user VPN with IKEv2 and the branch office VPN using IKEv2 when set up with a dynamic gateway peer.”
To assist users in identifying compromised devices, WatchGuard has provided indicators of compromise. They advise anyone detecting signs of unauthorized activity to change all locally stored secrets on affected firewalls. Additionally, WatchGuard offered a temporary workaround for network security personnel who are unable to promptly patch these devices. This includes disabling dynamic peer BOVPNs, implementing new firewall policies, and turning off default system policies that manage VPN traffic.
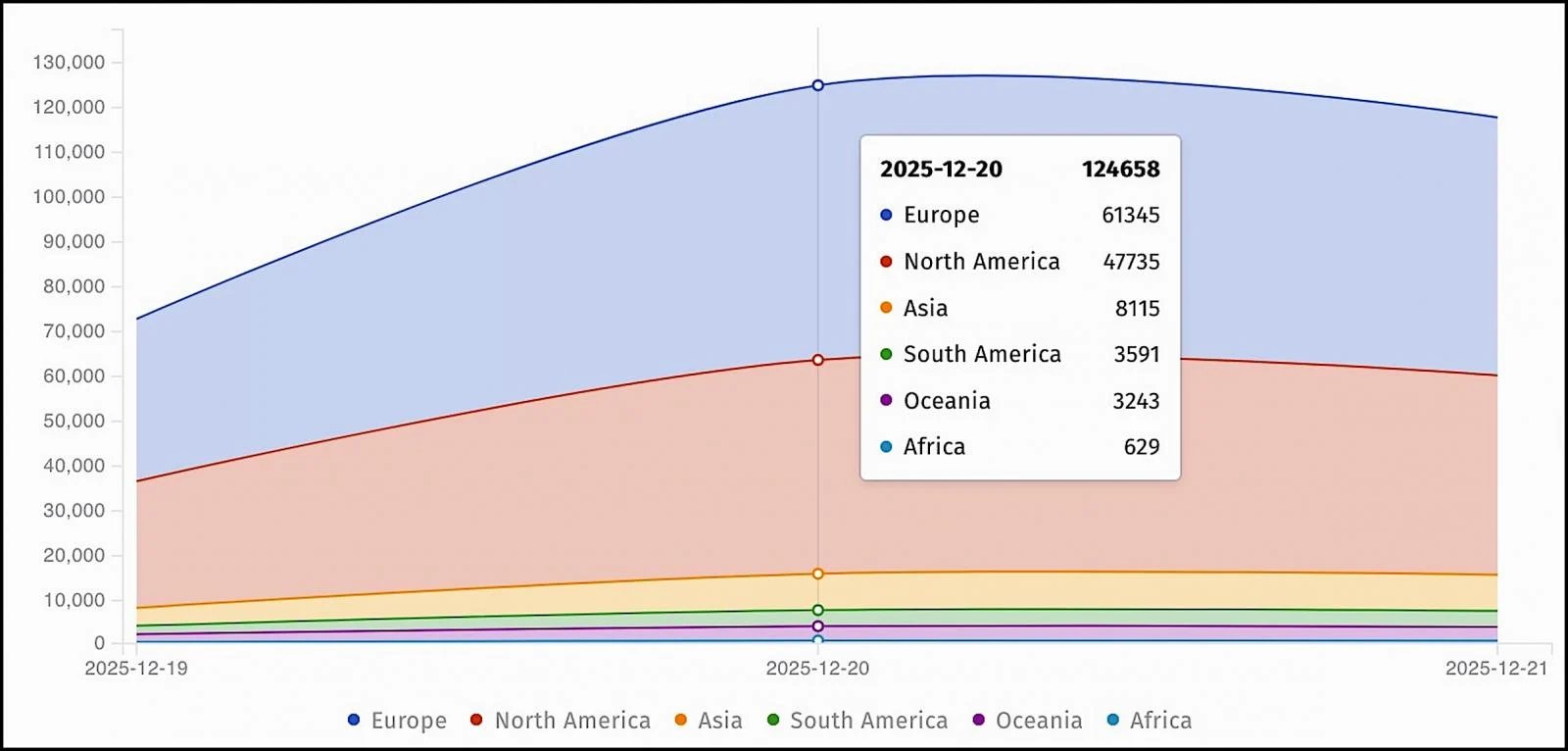
On Saturday, the cybersecurity group Shadowserver reported discovering over 124,658 unpatched Firebox instances exposed online, with 117,490 of these still exposed by Sunday.
The day after WatchGuard distributed the patches, CISA added CVE-2025-14733 to their Known Exploited Vulnerabilities (KEV) Catalog.
The United States cybersecurity authority has also mandated that Federal Civilian Executive Branch (FCEB) agencies must patch their Firebox firewalls within a week—by December 26th—following the directives of Binding Operational Directive (BOD) 22-01.
“This type of vulnerability frequently serves as an attack vector for malicious cyber actors and represents significant risks to the federal enterprise,” CISA cautioned. “Ensure mitigations are applied as per vendor guidelines, adhere to applicable BOD 22-01 guidance for cloud services, or discontinue use of the product if mitigations are not available.”
In September, WatchGuard addressed a similar RCE vulnerability (CVE-2025-9242) affecting Firebox firewalls. A month later, Shadowserver identified over 75,000 Firebox firewalls exposed to CVE-2025-9242 attacks, predominantly in North America and Europe. CISA subsequently classified this security loophole as actively exploited and ordered federal agencies to secure their Firebox devices from these ongoing assaults.
Two years prior, CISA had directed U.S. government agencies to address another actively exploited WatchGuard flaw (CVE-2022-23176) that affected Firebox and XTM firewall appliances.
WatchGuard collaborates with over 17,000 security resellers and service providers, securing the networks of more than 250,000 small and medium-sized enterprises globally.
Inadequate IAM isn’t merely an IT issue – its impact resonates across your entire organization.
This comprehensive guide discusses why conventional IAM practices struggle to meet contemporary demands, presents examples of effective IAM solutions, and includes a straightforward checklist for crafting a scalable strategy.