
- Home
- Managed Services
- Cyber Security
- Blog
- About Us

We 365 Admin Support, just simplify your IT problems
Call for a free support. +91 96666 59505Platform Partnership
- Who We Help
- Shop
- Contact
- News




Shadowserver, an internet security watchdog, has discovered more than 25,000 Fortinet devices exposed online that have FortiCloud SSO enabled. This revelation comes amidst ongoing attacks targeting a significant authentication bypass vulnerability.
On December 9, Fortinet announced it had patched the security vulnerabilities identified as CVE-2025-59718 (affecting FortiOS, FortiProxy, FortiSwitchManager) and CVE-2025-59719 (related to FortiWeb). Fortinet clarified that the vulnerable FortiCloud SSO login feature is not activated unless administrators register the device with Fortinet’s FortiCare support service.
A report from Arctic Wolf on Monday indicated that this vulnerability is being actively exploited, allowing malicious actors to compromise admin accounts through harmful single sign-on (SSO) logins.
Threat actors are exploiting this vulnerability in exposed products using a maliciously constructed SAML message to gain admin-level access to the web management interface, enabling them to download sensitive system configuration files. These files can reveal potentially vulnerable interfaces, hashed passwords, internet-facing services, network architectures, and firewall configurations.
Today, Shadowserver reported tracking over 25,000 IP addresses with a FortiCloud SSO signature, including over 5,400 in the United States and almost 2,000 in India.
Currently, there is no information on how many of these devices have been secured against attacks leveraging the CVE-2025-59718/CVE-2025-59719 vulnerabilities.
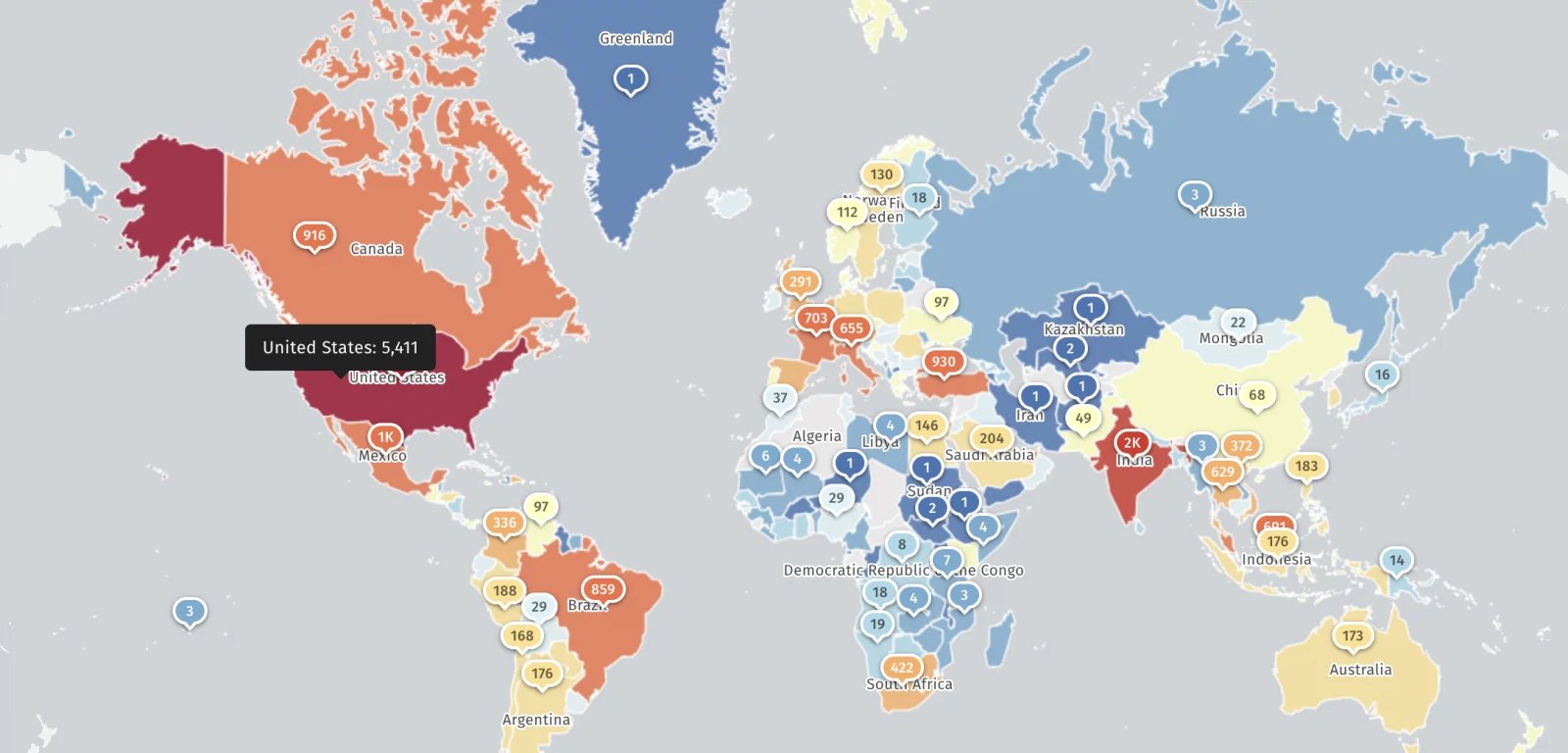
Macnica threat researcher Yutaka Sejiyama informed BleepingComputer that his scans identified over 30,000 Fortinet devices with vulnerable FortiCloud SSO activated, which also expose web management interfaces to the public internet.
“Given the frequency of past exploits against FortiOS admin GUI vulnerabilities, it’s surprising that so many admin interfaces are still accessible publicly,” Sejiyama stated.
This Tuesday, CISA included the FortiCloud SSO authentication bypass vulnerability in its catalog of actively exploited vulnerabilities, instructing U.S. governmental agencies to apply patches by December 23rd, as outlined in the Binding Operational Directive 22-01.
Fortinet vulnerabilities have often been targeted by cyber-espionage, cybercrime, or ransomware groups, frequently emerging as zero-day vulnerabilities.
In February, Fortinet revealed that the infamous Chinese Volt Typhoon hacking group had exploited two vulnerabilities in FortiOS SSL VPN (CVE-2023-27997 and CVE-2022-42475) to breach a Dutch Ministry of Defence military network using the custom Coathanger remote access trojan (RAT) malware.
Recently, in November, Fortinet advised of a FortiWeb zero-day (CVE-2025-58034) being exploited in the wild, shortly after confirming it had quietly patched another FortiWeb zero-day (CVE-2025-64446) that wasexploited in widespread attacks.
Issues with IAM can ripple across your organization, affecting not just IT but the entire business.
This practical guide explains the shortcomings of traditional IAM practices in addressing modern challenges, provides examples of effective IAM strategies, and includes a simple checklist for building a scalable plan.